Cybersecurity Services
Is the timing right to outsource your cybersecurity?
What business outcomes are you looking to achieve?
Thrive can help.
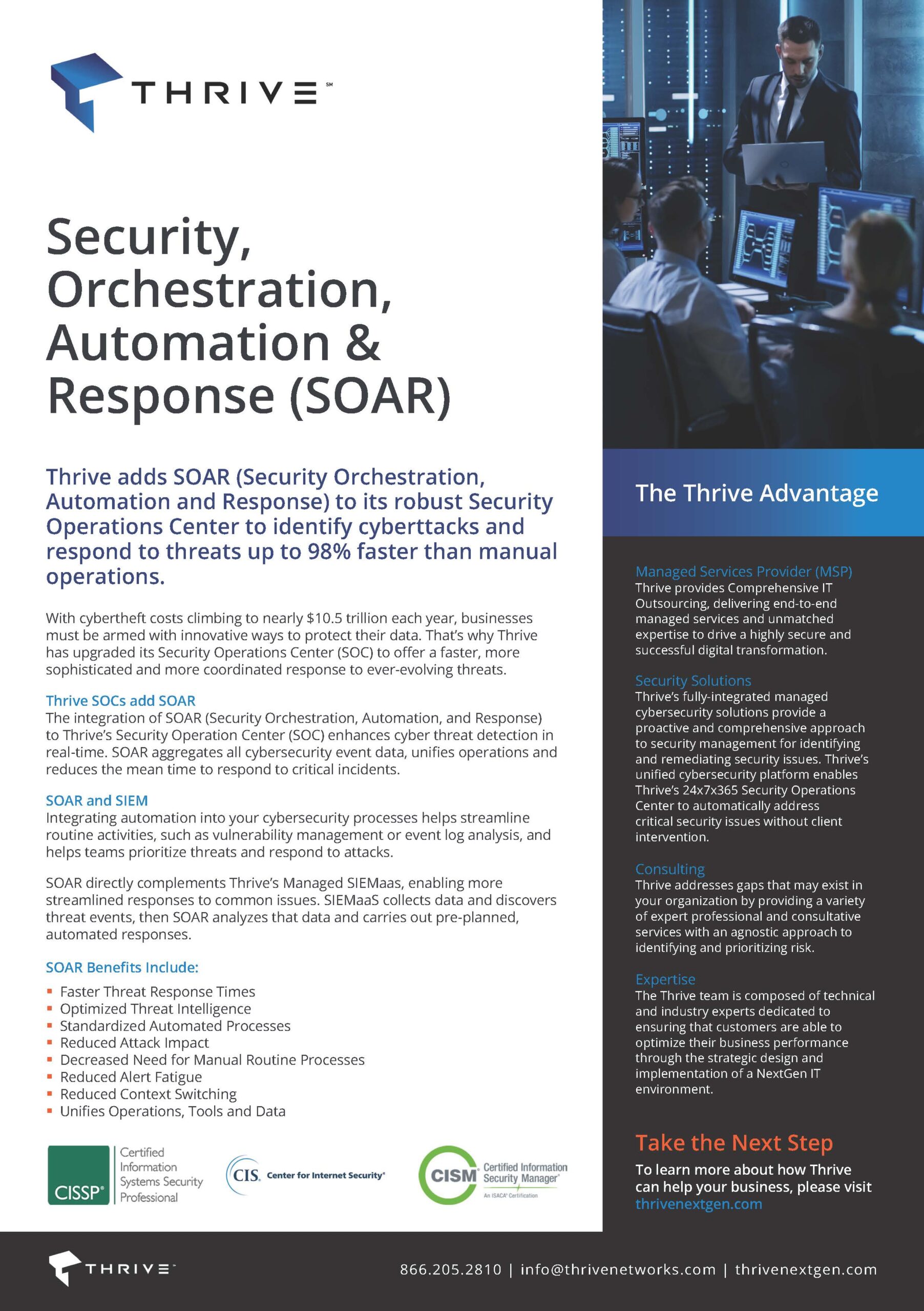
Complex cyber risk mitigation, simplified. Today’s complex cyber threats require a multi-solution approach combined with advanced skill sets and real-time, 24/7 monitoring. Thrive’s leading security platform integrates best in breed technologies, analyzing attack data with AI and certified security analysts to prevent the impacts from threats allowing you to focus on critical business outcomes.
Our security team combines the power of automation for rapid response and remediation with the expertise of our staff to address complex issues intelligently.
Report: Iran Conflict Cyber Operations and Global Implications
Military escalation is often accompanied by coordinated cyber activity conducted by nation-state actors and affiliated groups seeking to gather intelligence, disrupt adversaries, and position themselves strategically in the global cyber domain. To help organizations prepare for this evolving threat landscape, Thrive’s Cybersecurity Incident Response Team (CIRT) has published a new intelligence report which analyzes how the current geopolitical escalation involving Iran is influencing cyber activity globally and what it may mean for organizations operating across critical industries.
Trusted Cybersecurity Partners
Thrive offers NextGen cybersecurity solutions and services designed to meet the needs of your business.
Threat Detection and Response
IT and business leaders need to have advanced technology combined with human expertise to keep their businesses safe from evolving threats. Thrive’s threat detection and response services provide your business with real-time detection of threats and rapid response by our security experts to investigate, contain, and mitigate security incidents.
Backed by our 24/7/365 Security Operations Center (SOC), Thrive’s Managed Detection and Response (MDR) and Endpoint Detection and Response (EDR) services provide you with the confidence that your critical systems are monitored around the clock.
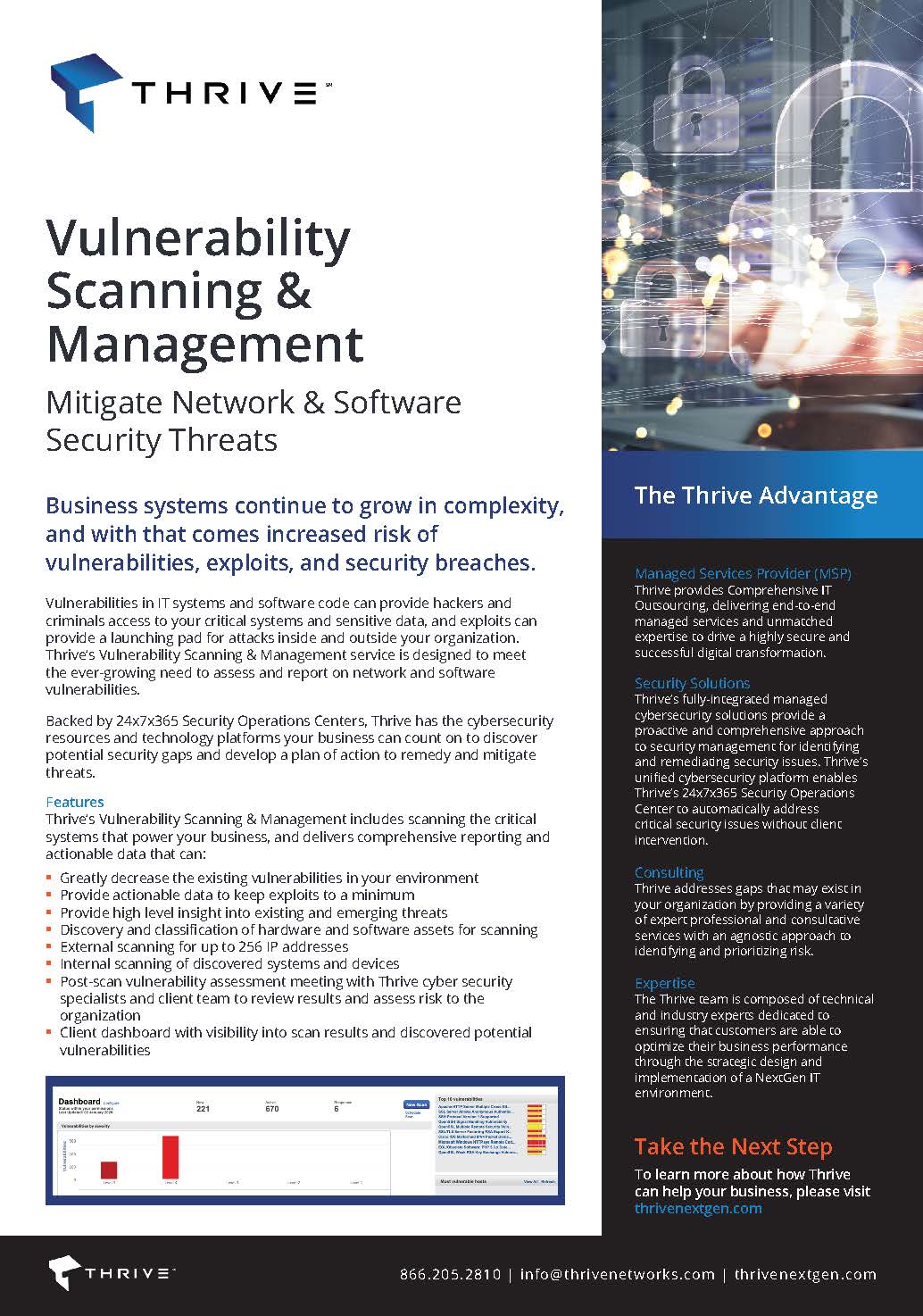
Attack Surface & Risk Management
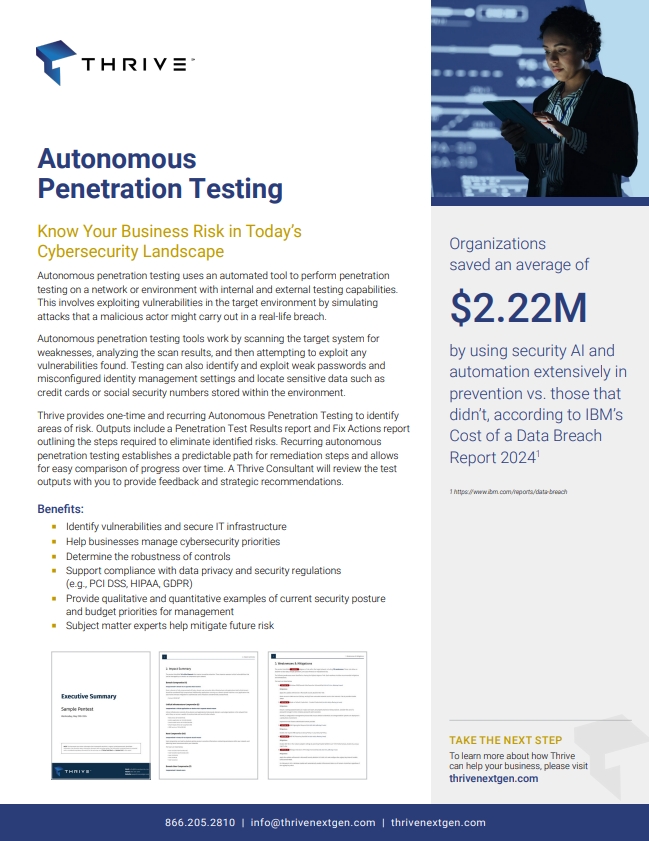
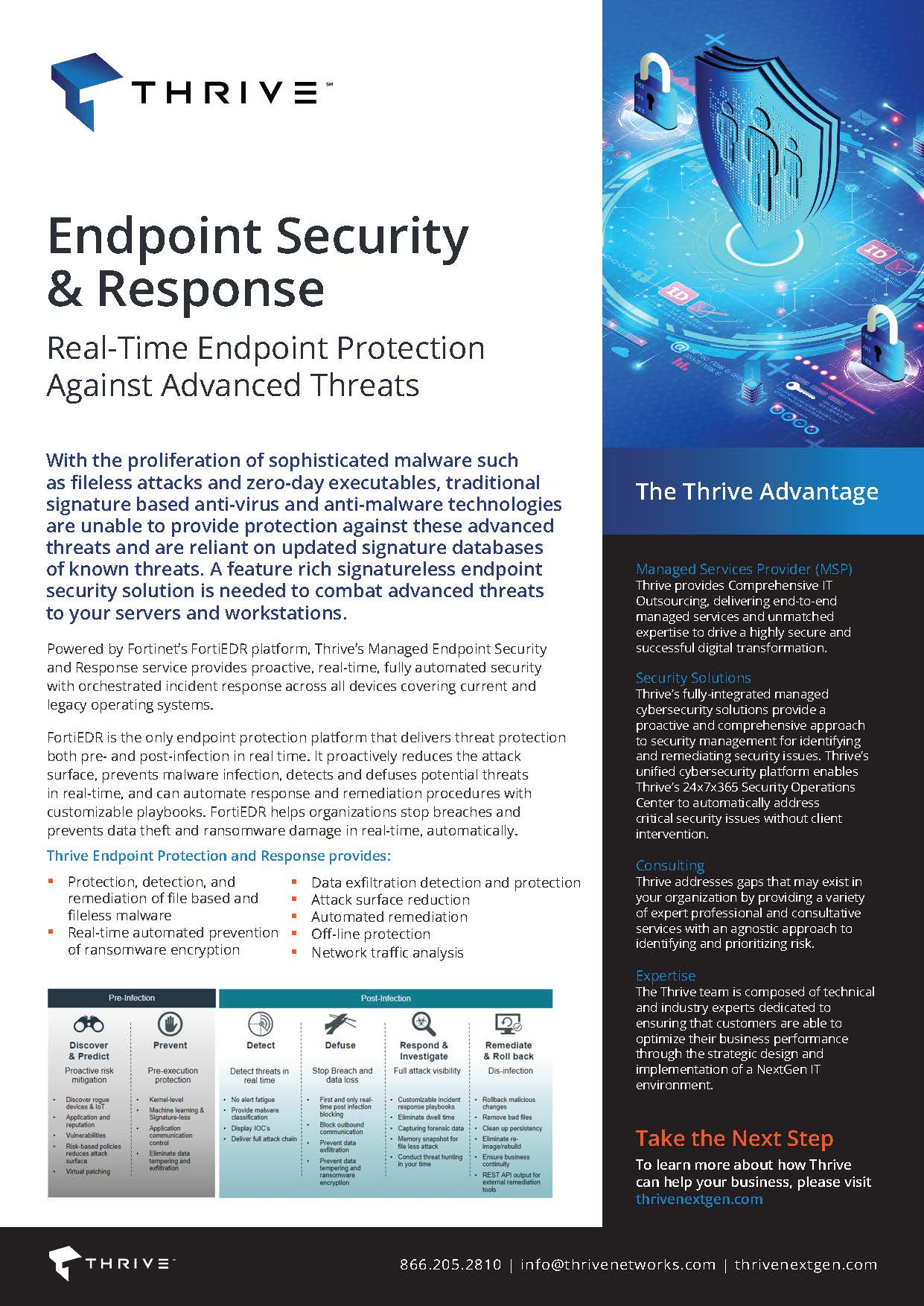
Thrive’s attack surface management services can help your business implement a continuous threat exposure management program that identifies potential entry points and actively remediates them. Proactive services include vulnerability management and autonomous penetration testing to discover weaknesses, dark web monitoring to identify external risks, and patch management to remediate software vulnerabilities. Stay ahead of emerging threats with our automated technologies and expert-guided strategies.
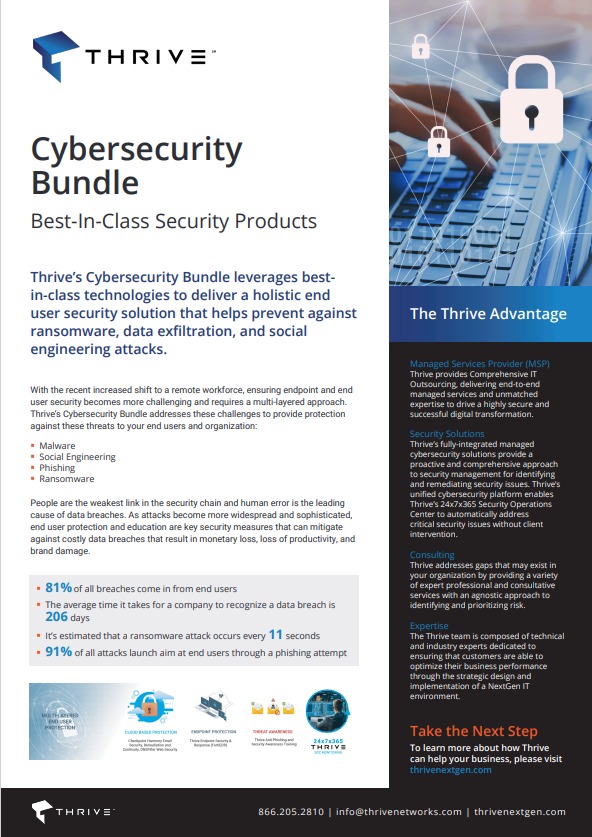
End User and Workstation Security
End-user and workstation security is critical to safeguarding your operations by preventing unauthorized access and mitigating threats at the individual device and account level. Thrive offers robust protection through EDR, email security, and DNS web filtering that continuously protects both users and their workstations from evolving cyber risks.
And with Thrive’s anti-phishing and security awareness training, you can ensure your employees understand the mechanisms of spam, phishing, spear phishing, malware, ransomware and social engineering to improve awareness of and response to security threats.
Incident Response and Remediation
Thrive Incident Response & Remediation provides on-demand security response services to contain and remove threats, along with engineering assistance to rebuild and restore critical systems. The service provides faster recovery time from a cybersecurity incident so that the costs associated with business disruption are minimized.
With a Thrive Incident Response Retainer in place, companies can benefit from the Thrive team’s preparation, expertise, and responsiveness through:
- Pre-Incident Planning
- Incident Response Tools
- Compromise Assessment
- Prioritized Incident Management
Security for Microsoft 365 & Azure
Get the most out of your investment in Microsoft licenses by leveraging Thrive to ensure your Microsoft security tools like Defender, Sentinel, and Entra ID are optimized to protect your devices, user accounts, identities, and cloud workloads.
From upfront and ongoing governance and compliance to proactive monitoring and advanced threat detection, your business can benefit from seamless integration between Microsoft’s security features and Thrive’s 24×7 Security Operations Center, helping your team stay secure without disrupting productivity.
Security Advisory & Consulting
Thrive’s Security Advisory & Consulting services align cybersecurity strategies with business goals by delivering your organization expert guidance on cybersecurity services, risk management, and regulatory compliance. From tailored assessments to support from our team of virtual CISOs, you can receive actionable insights and customized solutions to fortify your defenses and address evolving security challenges within your budget and timelines.

Driving Better Business Outcomes
“I can’t overstate how impressed we were with Thrive’s approach. The efficiency and expertise they brought to the table was remarkable.”
– John Ross, CIO, EXO Inc.
Hear from Our Customers
Managed Cybersecurity Services and Solutions for Your Business
From endpoints to the Cloud and everything in between, Thrive’s dedicated security experts design and deploy the ideal security services to meet your unique needs. Our tailored cybersecurity solutions ensure end-to-end protection for your systems and data, relieving the burden on your internal IT teams.
With Thrive as your managed security services provider, you will be one step ahead of potential threats. We combine the power of automation for rapid response, the expertise of our staff, and our 24x7x365 Security Operations Centers (SOC) to address complex issues intelligently.
Thrive's Cybersecurity Mesh Architecture (CSMA)
Thrive supports clients and their ever-changing threat surface by constantly evaluating and improving our people, processes, and the technologies that are connected through our cybersecurity mesh.
Thrive’s Cybersecurity Mesh Architecture reduces gaps by connecting siloed solutions with two-way integrations that pull data into the mesh and push actions out to a wide range of tools. Thrive’s cybersecurity mesh includes threat intelligence and integrated defense tools to anticipate and prevent attacks. Using automation and orchestration, Thrive adds more context and faster connections between tools so that enforcement decisions align with the speed of business.
What Is Your Security Risk Exposure?
Did you know it takes organizations around 6 months to identify breaches? Reducing this threat exposure is critical for:
- Protecting sensitive information
- Preventing financial loss
- Maintaining business continuity
- Meeting compliance and legal requirements
Thrive can help companies lower their security risk by reducing the likelihood and impact of security incidents, while meeting legal and operational obligations.


Why Companies Outsource with Thrive
Thrive takes a customer-first cybersecurity approach. When entrusted to fully manage a customer’s IT environment, from security, to collaboration, to the Cloud, Thrive enables often short-handed IT teams to focus on delivering results to core business operations.
As a single point of control and communications across the IT landscape, Thrive can address issues without the coordination of multiple vendors as Thrive brings all of the pieces to the puzzle together.
Give Your Business the Thrive Cybersecurity Advantage
- 24×7 Security Operations Center:
A dedicated, in-house SOC organization that does not rely on 3rd-party services that can create gaps in response time and accountability - Scale and Experience:
Security experts with decades of experience serving complex mid-market organizations and highly regulated industries
- End-to-End Managed Services
Comprehensive MSSP cybersecurity services combined with MSP support to directly mitigate and remediate security incidents - Thrive Platform
Security orchestration and automation that integrates threat intelligence, case management, and reporting
Frequently Asked Questions
How do you protect our business from the biggest cyber risks today?
We protect your business from cybersecurity risks by deploying multi-layered security solutions, including endpoint detection and vulnerability management. Continuous monitoring ensures emerging threats are detected and mitigated early.
Can you help us balance security investments with budget priorities?
Yes, we prioritize high-risk areas and implement cost-effective solutions that maximize protection without overspending. Our approach aligns security with your business objectives.
How do you make sure our company stays resilient if an attack happens?
We combine proactive, round-the-clock monitoring with incident response and remediation, along with regular testing, so your business can continue operating and recover quickly from incidents.
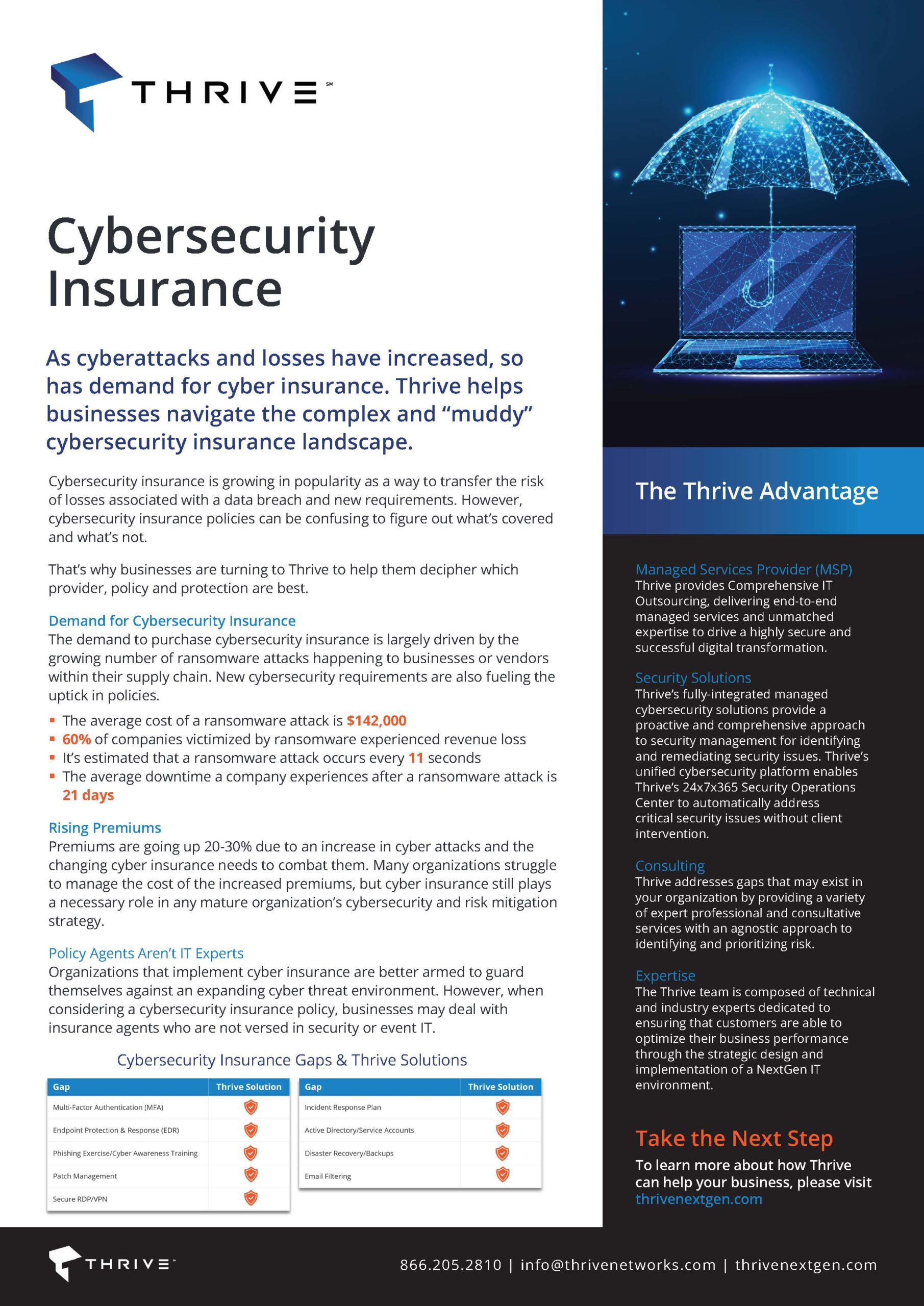
Will your cybersecurity services meet requirements from regulators and insurers?
Absolutely. Thrive’s services are designed to align with industry regulations and cybersecurity insurance standards, helping ensure compliance and coverage readiness.
How do you ensure we’re not falling behind as threats evolve?
We continuously update security measures, integrate threat intelligence, and conduct periodic assessments to keep your defenses current against emerging risks.
What’s the long-term business value of partnering with Thrive on cybersecurity?
Partnering with Thrive reduces operational risk, protects revenue, and builds trust with customers and stakeholders. It also frees internal teams to focus on growth initiatives rather than firefighting threats. Thrive takes a layered approach to security so that your security infrastructure is tailored to your business needs and goals.
Is there a way to test our security posture?
Yes, we offer penetration testing, vulnerability assessments, and simulated attacks to identify weaknesses and recommend actionable improvements.
Thrive Certifications

Thrive delivers NextGen Managed Services designed to optimize business performance, ensure scalability, and future-proof digital infrastructure operations. We have achieved the following certifications across our global regions:
| Certification | Type/Scope | Operational Area |
| SOC 2 Type 2 & SOC 3 | Trusted Services Criteria for Security and Confidentiality | North America (United States and Canada) |
| ISO27001:2022 | Information Security Management | United Kingdom |
| ISO9001:2015 | Quality Management | United Kingdom |
| Cyber Essentials (CE) / Cyber Essentials Plus (CE+) | Cybersecurity | United Kingdom |
Cybersecurity Resources
Ready to Speak with Our Cybersecurity Experts?
Contact Thrive today and learn how we can deliver continuous, round-the-clock protection against both everyday and emerging threats, safeguarding your business’s productivity.