Office 365
Balancing Security and Productivity in Microsoft 365 During Times of Crisis – Part 2
In our first blog of this series, we discussed how entitlement management in Azure Active Directory (Azure AD) Identity Governance creates Access Packages to control the scope and duration of access to groups, applications, and SharePoint sites. The two additional primary tools designed to control and audit access to company resources include Access Reviews and Privileged Identity Management. These three functions work synergistically to help keep a watchful eye on the collaboration space without impeding productivity.
In Part 2, we’ll discuss Access Reviews in detail. These are about auditing access to ensure previously-granted permissions are still appropriate and necessary.
Access Reviews
Setting up an Access Review
An Access Review is a scheduled, guided review of a group of Microsoft 365 users to help determine if their continued access to tenant resources is required. The review can be performed by multiple users and can be set to report on dispositions and, in some cases, automatically take action based on the dispositions set.
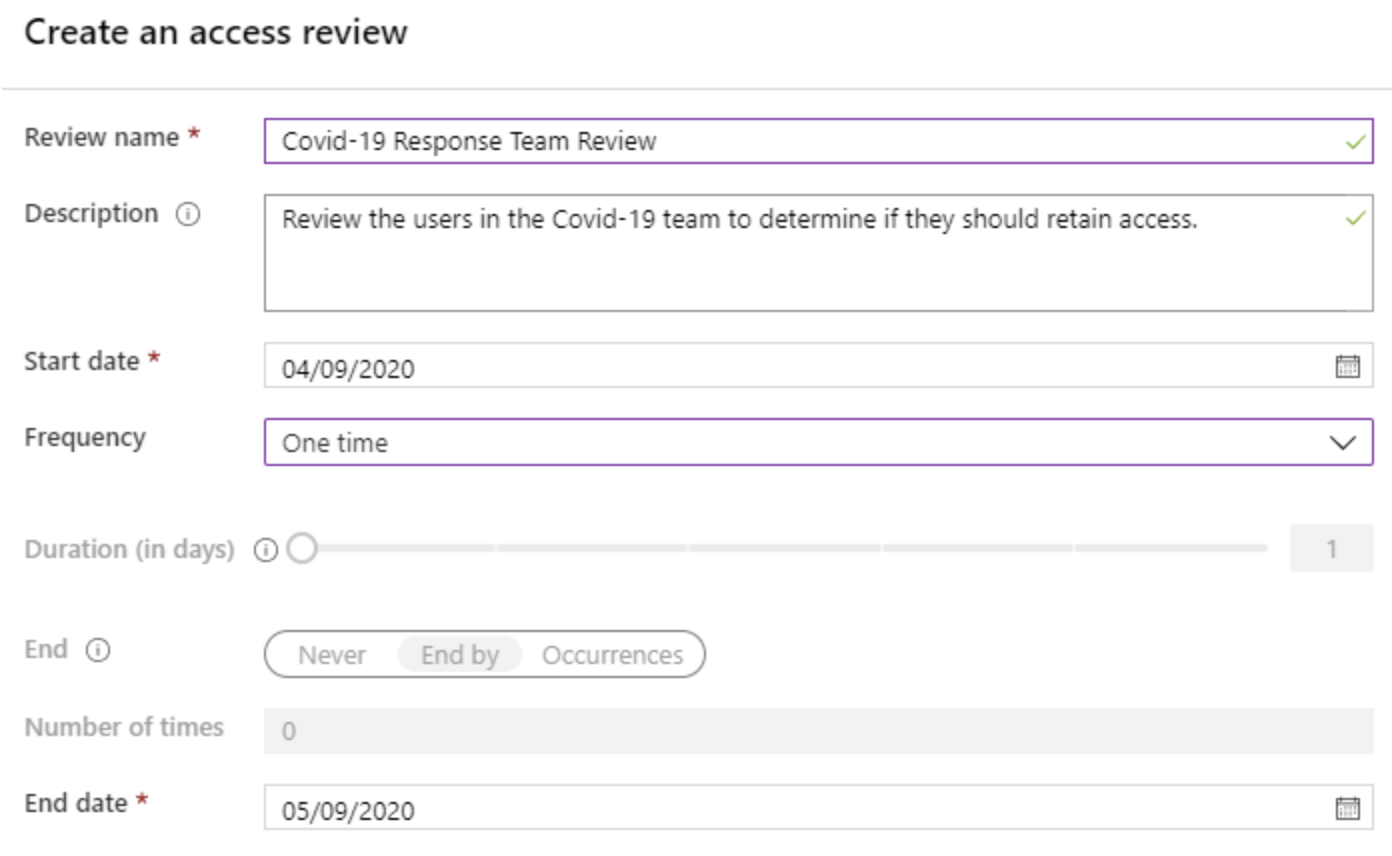
The first step of creating an Access Review is naming and describing its purpose. You will also set a start date and frequency if the intention is to perform the review periodically. Frequencies include weekly, monthly, quarterly, semi-annually, and annually. Occurrences can run indefinitely or can end by a specified date or after a number of occurrences. The review will also have an end date, after which the review will close and the “upon completion settings” will be applied.
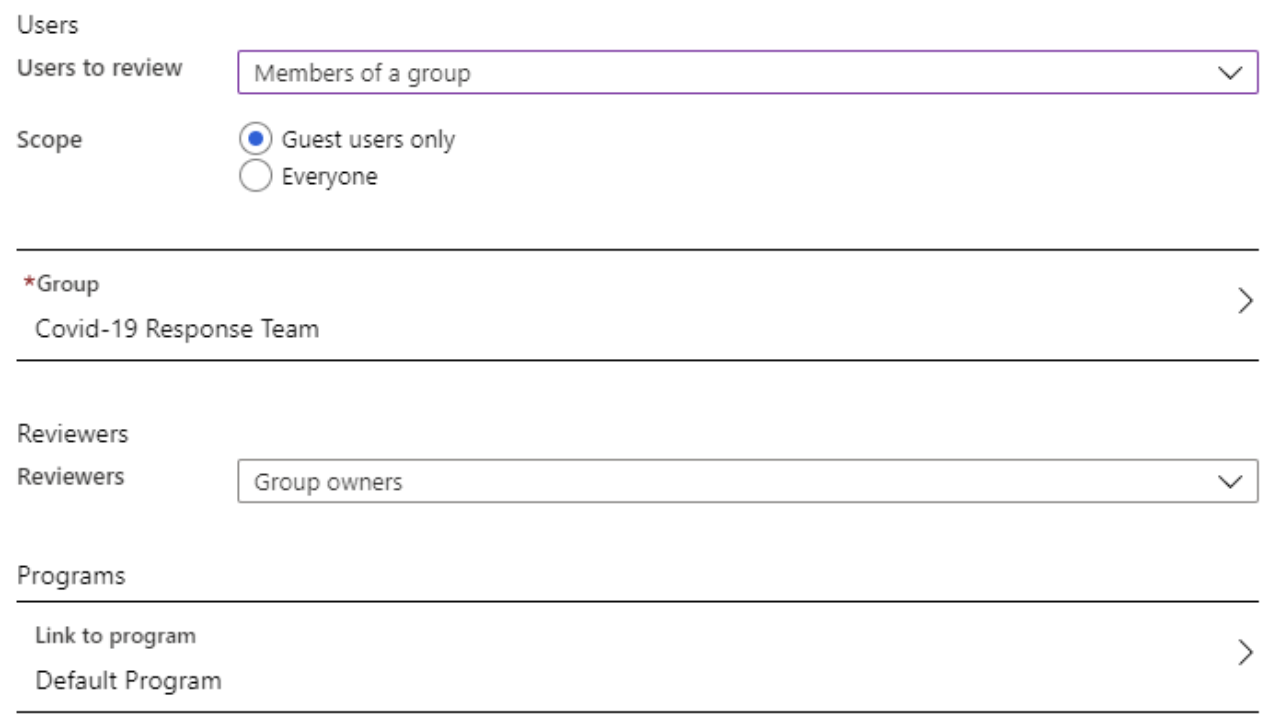
Next, you determine who will be reviewed and who will be performing the review. The users to review can be Members of a Group or users Assigned to an Application on the tenant. Additionally, you can scope the review to include Guest users only or include all users. For Reviewers, you can select the Group’s owners, specific tenant users, or allow for self-review by the users. You can also associate the review with a Program (similar in concept to a Catalog for Access Packages) or choose the Default Program.
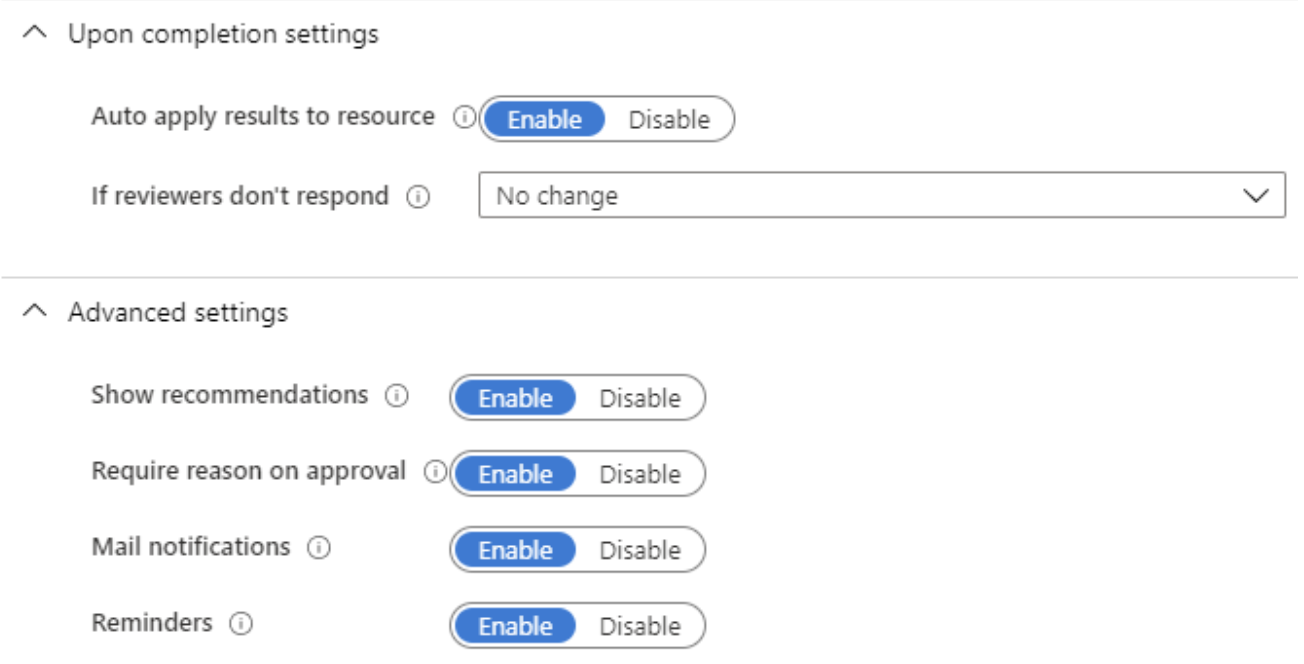
Next, we’ll set the “Upon completion settings,” which determine the action to take when the end date of the review is reached. The first choice is whether or not you’d like to auto-apply the results. With this setting enabled, any user whose disposition is to Deny access will automatically have their access removed upon the completion of the review. The second option is to determine what actions to take if reviewers don’t respond. These options include “No change,” “Remove access,” “Approve access,” or “Take recommendations.” The last option is based on Azure AD’s auto-set recommendations, which are primarily based on the last time the reviewed user utilized the system.
The final settings, under Advanced, include options to Show recommendations, Require a reason on approval, Mail notifications, and send Reminders to reviewers. All are currently enabled by default.
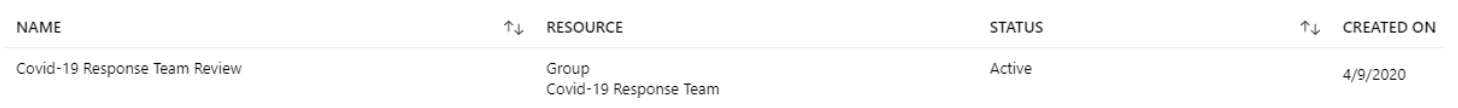
At this point, we are ready to start the review process. After pressing the Start button, the new Access Review will be added to the Access Reviews section within the Identity Governance module. The listing will include the name, the resource being reviewed, the status, and when it was created.
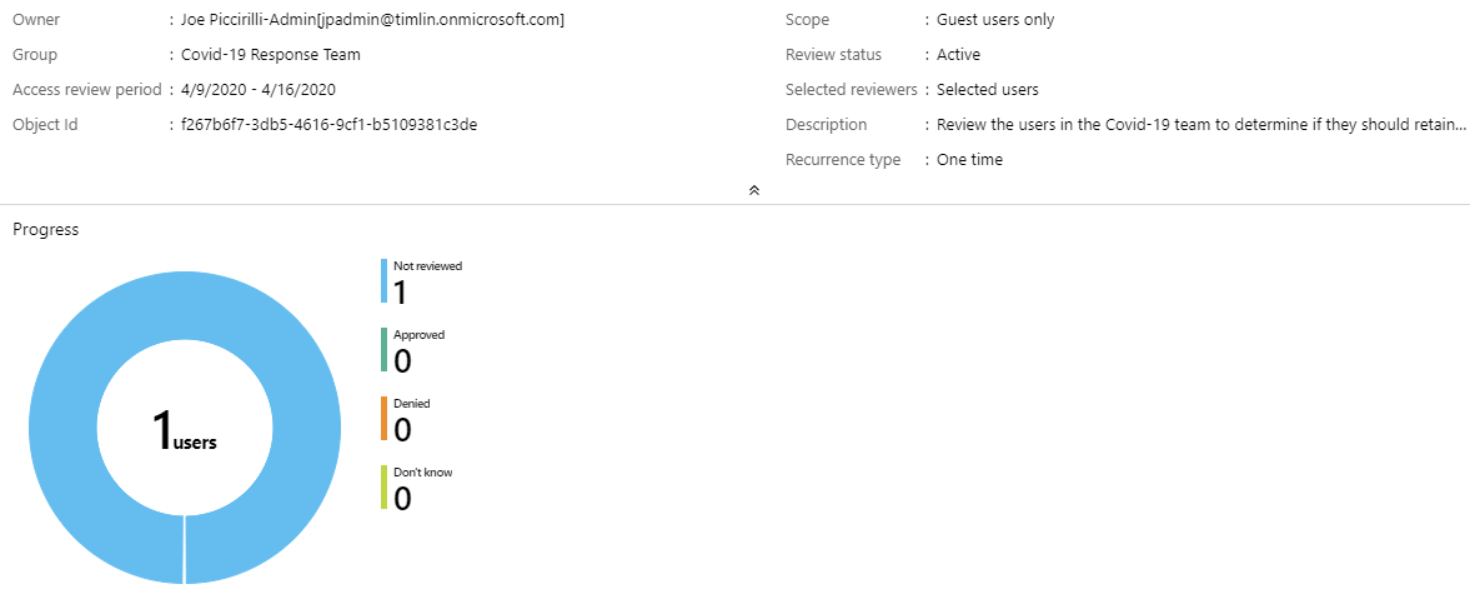
Clicking on the review will show an overview of the settings as well as a chart showing the status of the resources being reviewed. There are also pages to view the Results and the Reviewers. You can even send automated reminders for individual reviewers with the press of a button.
Performing a User Access Review
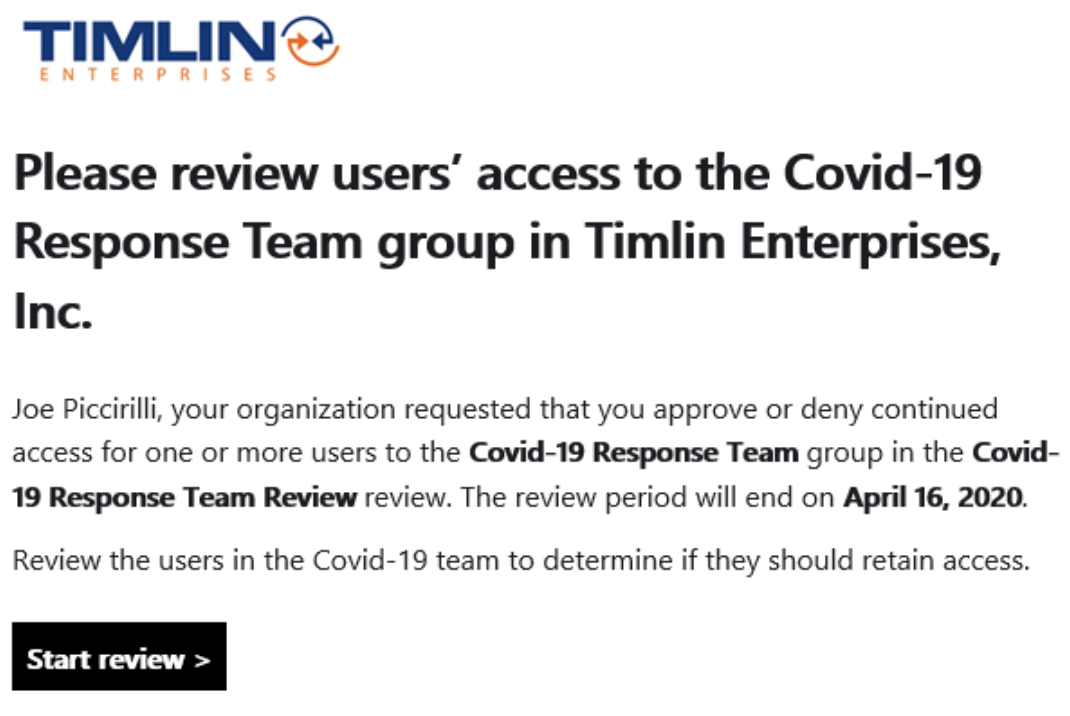
If the Mail Notifications option was set to Enabled, reviewers should receive an email with a link to begin their review. The email will have a hyperlinked button to take the user directly to the review page.
The Review page will show all relevant information, including who requested the review, when it is due by, the names of any other reviewers, and the progress made so far. It will also list each Resource being reviewed with their name, email address, Access Info (statement about whether they have recently logged in), and a recommended Action.
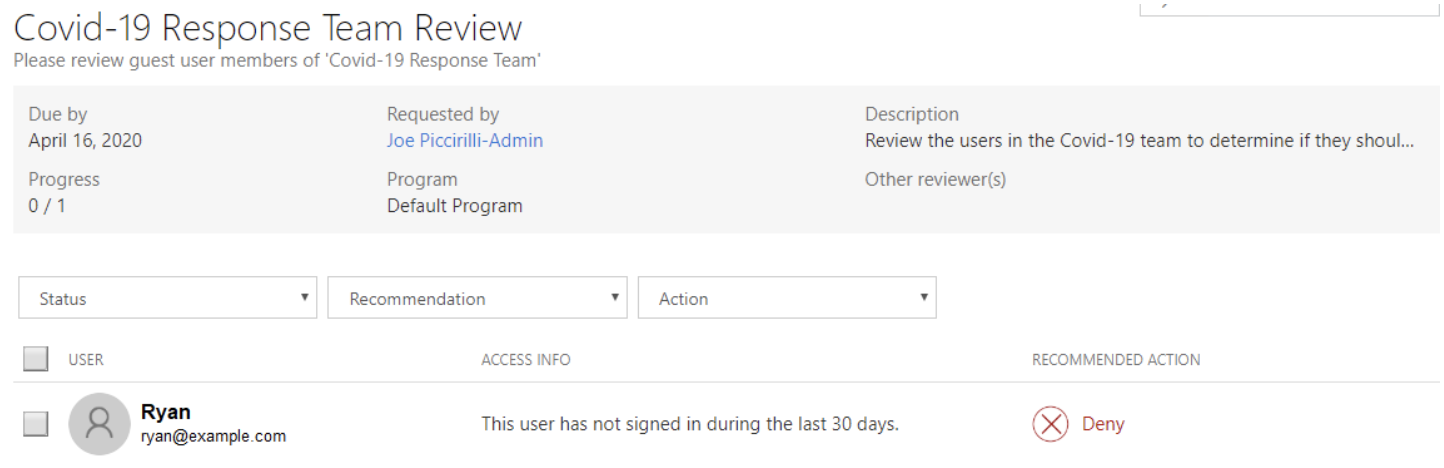
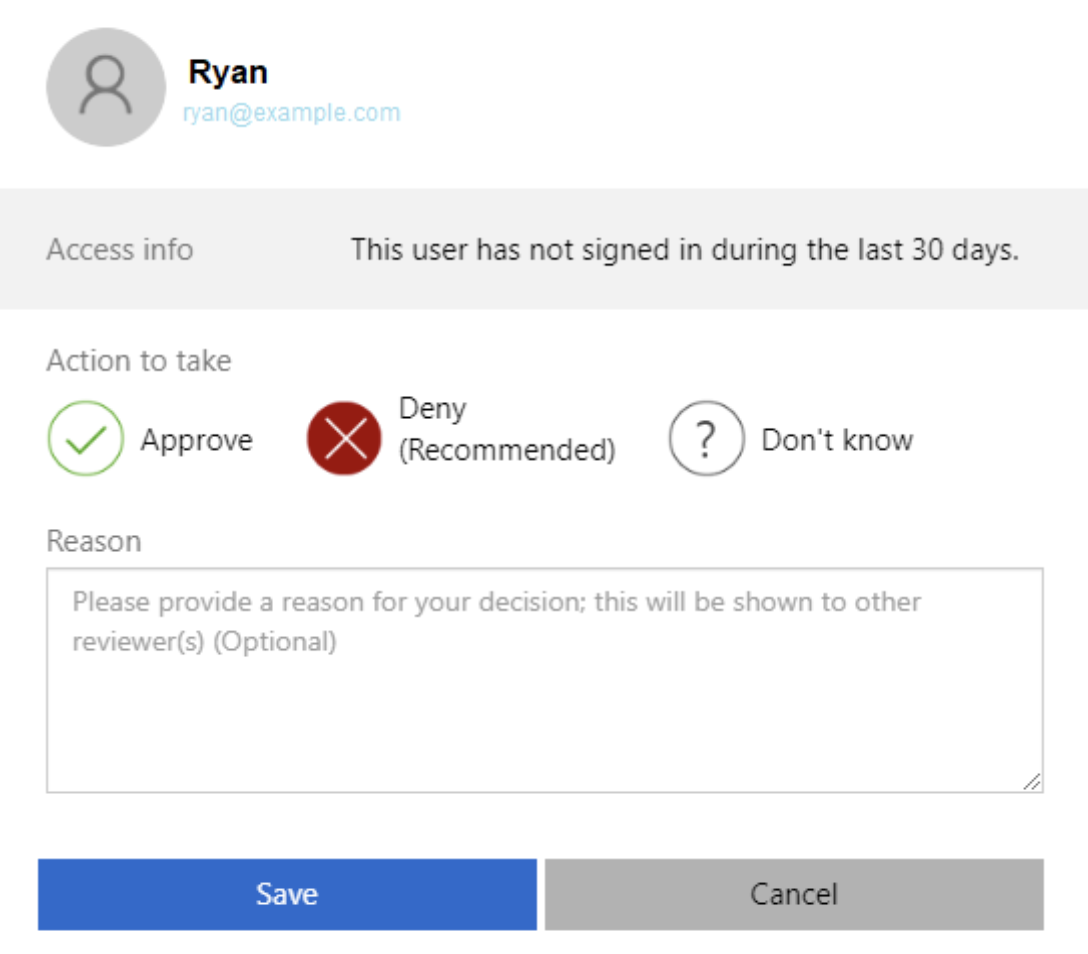
This list of users can be filtered based on Status (Reviewed, Not Yet Reviewed, All), Recommendation (Approve, Deny, All), or Action (Approved, Denied, Don’t Know, All). The reviewer can click on a single source to review or multi-select resources using the checkboxes, then press the “Review n user(s)” button. Reviewing resources opens a dialog with options for the disposition and comments. Actions can be Approve, Deny, or Don’t Know. The recommended action will be highlighted already. Don’t Know is useful if there are other reviewers who may have more insight or knowledge of the resource being reviewed.
Although all Resources may have been reviewed, the Access Review will stay open until its end date has been reached to allow for changes or other reviewers to provide input. If desired, a review can be manually stopped so action can be taken. This can be done by the user who originally set up the review using the Access Review overview screen. At that time, the actions will be automatically applied if the “Upon completion” setting’s “auto apply results to resource” is enabled, or the Apply Results button can be pressed if not.
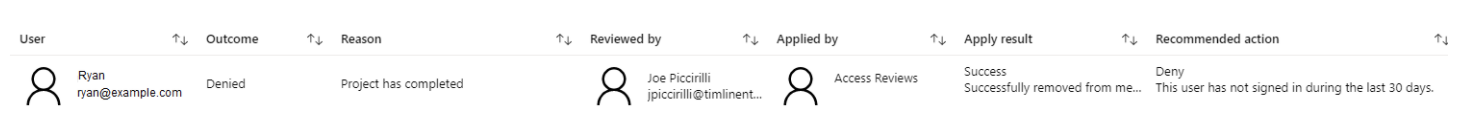
The results of the review can be reviewed in the Results section of the Access Review.
Summary
Access Reviews in Azure AD Identity Governance provide a simple, consistent, and governed method of reviewing and controlling access to company tenant resources. By combining Access Reviews with Access Packages, administrators can tightly control who has access to which resources and ensure they retain the appropriate access only as long as required, all while maintaining agility and simplicity for users.
Next up: Privileged Identity Management. Configure just-in-time role escalation to implement a least-privileged security model for day-to-day operations while providing a rapid but governed path to escalated roles as required. Stay tuned!
