Office 365
Balancing Security and Productivity in Microsoft 365 During Times of Crisis – Part 1
How Azure Active Directory (Azure AD) Identity Governance can assist your organization in responding quickly to new collaboration needs while maintaining security and governance.
The sudden onset of the COVID-19 pandemic sent much of the world into a frenzy. With businesses concerned for the safety and wellbeing of their employees and customers, and many governments strongly advising social distancing, the need to ramp-up the remote workforce went from a distant goal to a top priority almost overnight. One of the many groups greatly impacted by this new priority is the group of people responsible for collaboration platforms such as Microsoft 365. The need to quickly enable remote workers has made it seem necessary for many groups to ignore or postpone best practices and security considerations in favor of business continuity. Azure AD’s Identity Governance is one set of tools designed to help strike the balance between security and productivity, enabling quick turnaround on required resources while providing checks and balances to mitigate risk.
What is Azure AD Identity Governance?
Simply put, Azure AD Identity Governance is about “ensuring the right people have the right access at the right time.” More specifically, it is a set of 3 primary tools designed to control and audit access to company resources.
Entitlement Management is about creating Access Packages to control the scope and duration of access to groups, applications, and SharePoint sites.
Access Reviews are about auditing access to ensure previously granted permissions are still appropriate and necessary.
Privileged Identity Management covers the just-in-time elevation of tightly scoped roles to allow users to perform privileged operations when needed while maintaining lower permission levels during their day-to-day job functions.
These three functions work synergistically to help keep a watchful eye on the collaboration space without impeding productivity. Part 1 of this series will cover Entitlement Management in detail.
Entitlement Management
Setting up an Access Package
The key component of Entitlement Management is the creation of “Access Packages”. An Access Package is a collection of resources that users can be granted or request access to. Unlike simply adding users directly to Groups, these packages can control the duration, approval process, and periodic reviews of those assignments.
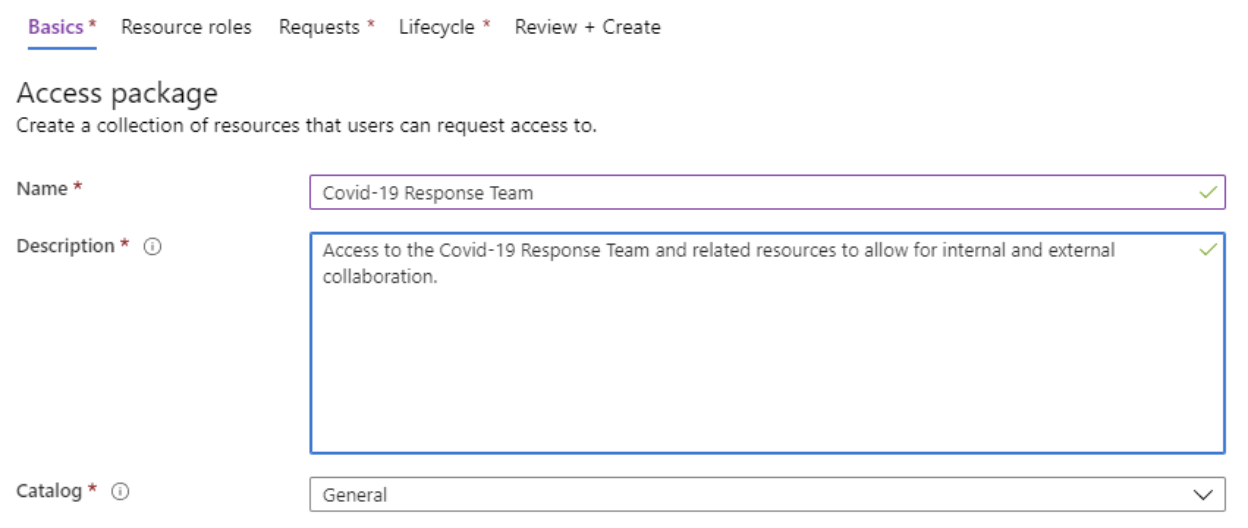
The first step of creating an Access Package is naming and describing its purpose. You can also create “Catalogs” to group multiple packages and delegate the administration of them to the appropriate users.
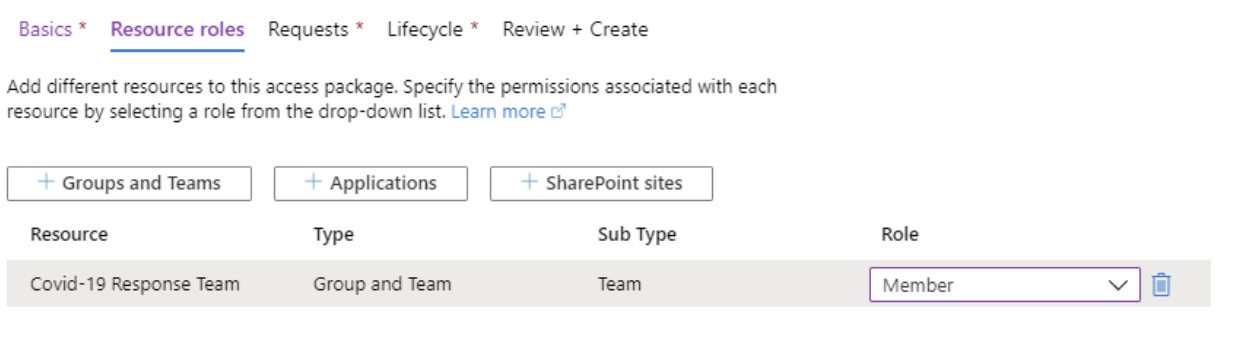
Next, you determine the Resource Roles that will be part of this package. It can be a combination of Groups/Teams, Applications, and SharePoint sites. In this case, we will grant access to the “COVID-19 Response Team” team in the Member role.
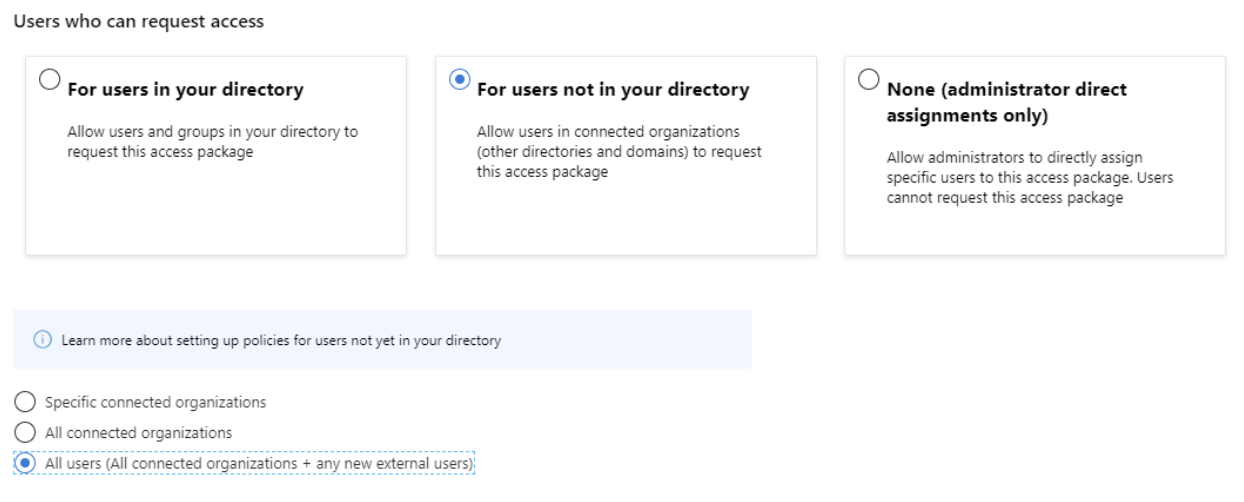
We’ll then move onto the Request process. Since this team may be made up of external collaborators who are unknown at this time, we’ll select “For users not in your directory”, and we’ll allow “All users (All connected organizations + any new external users)” to request access.
Since we are allowing as of yet unknown external users, we must require approval (other settings allow you to disable approval). We will set a specific user to provide approval, ensure a decision is made within 2 days, and force both the requestor and the approver to provide a justification for the access. We’ll enable this access request when we are ready to start requesting access.
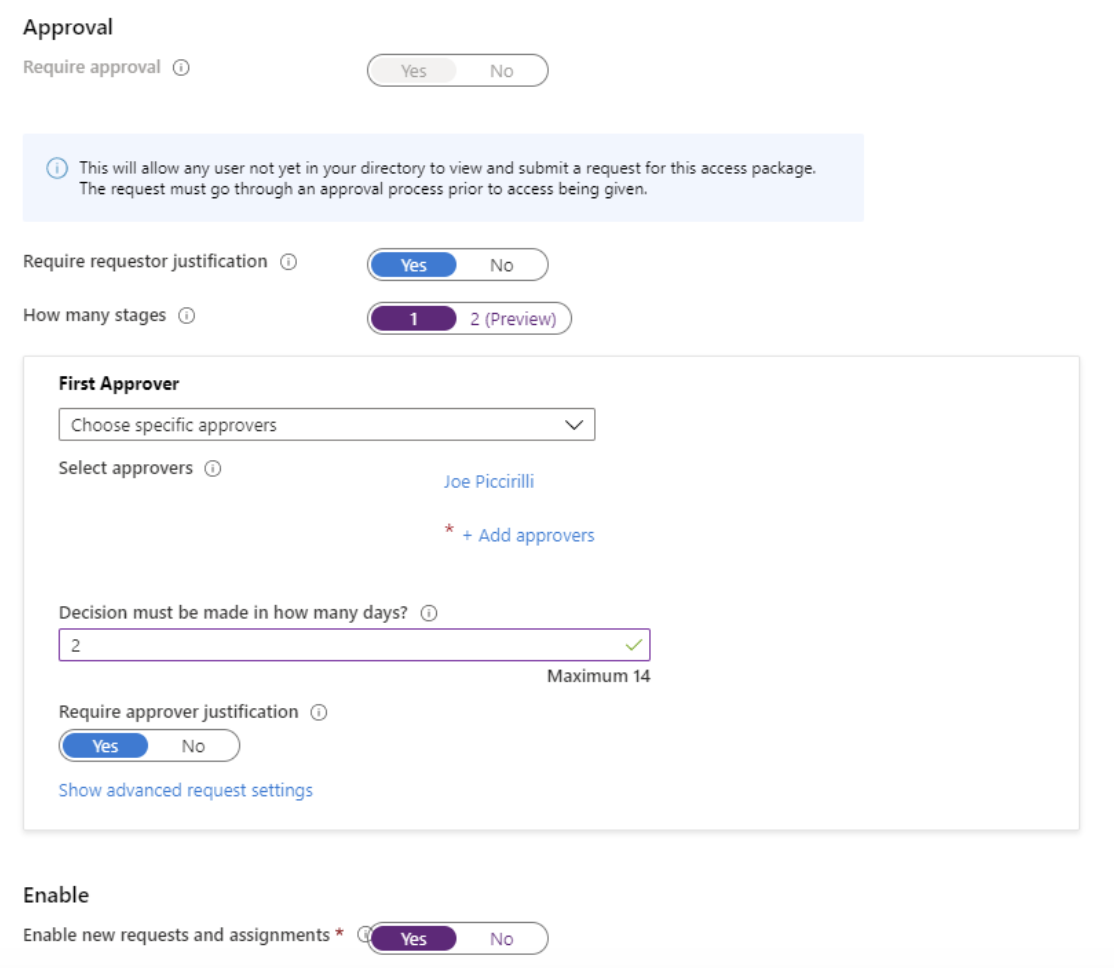
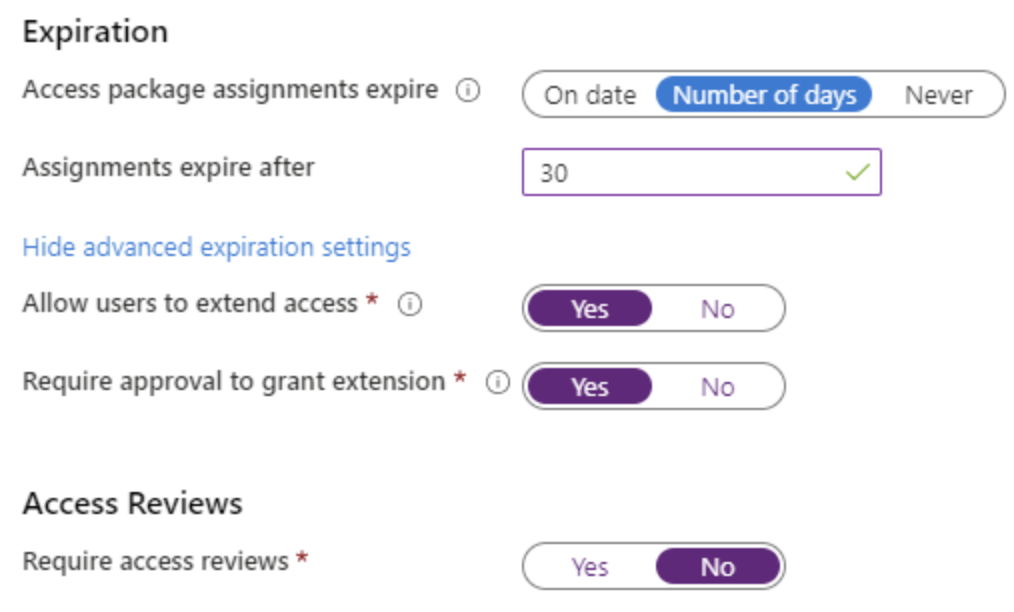
Next, we will set the lifecycle of the access being provided. In this case, we will allow for 30 days of access, with the ability to request an extension (which also requires approval). If this was a longer duration or did not expire, we could also tie access to an Access Review, which we’ll cover later.
The last page will show a summary of all the choices to allow you to make any desired changes before creating the package.
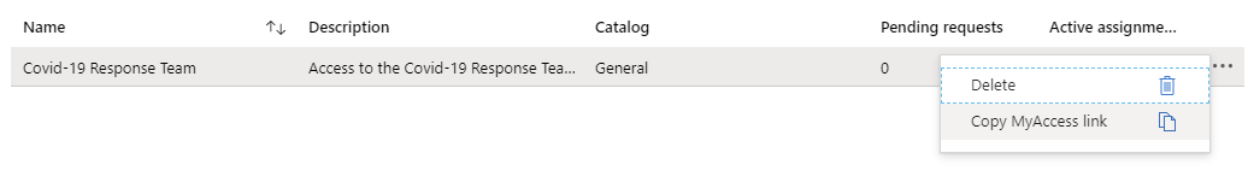
Once the package is created, the browser will display a list of all Access Packages the current user has access to. From here, you can use the ellipsis to copy the link used to request access. This link can be emailed, put on a public site, or shared in any other traditional way.
Requesting Access
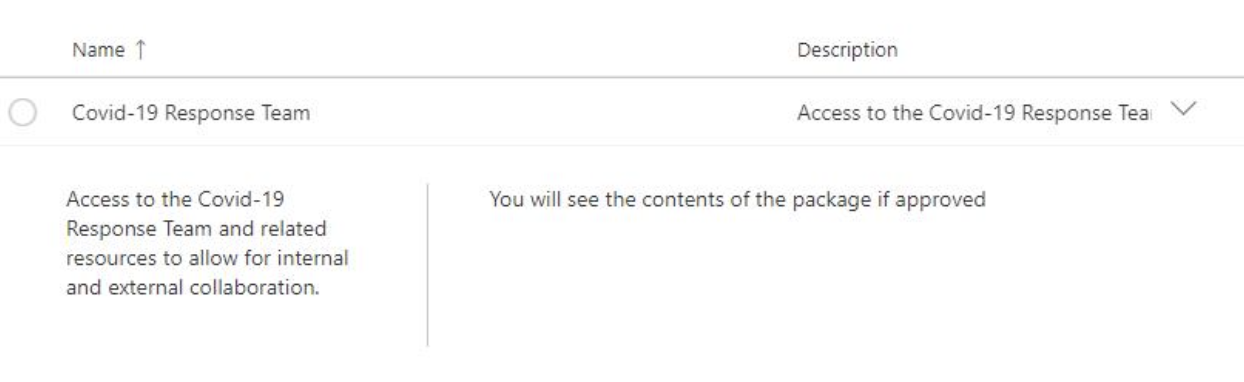
To request access via an Access Package, a user can use the link generated during the creation process. Once they sign in to the 365 tenant, they will be presented details of the access being requested. The user would then select the package and push the “request access” button.
From there, because we require justification, the user will be presented an area to provide the reason they are requesting access.

They will receive confirmation that their request was submitted.
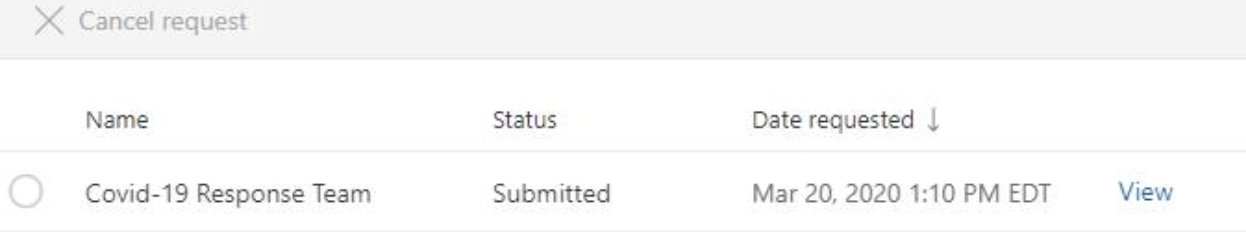
Approving Access
After requesting access, the Approver will receive an Email with actions to Approve or Deny the request, and a summary of the information about the request.
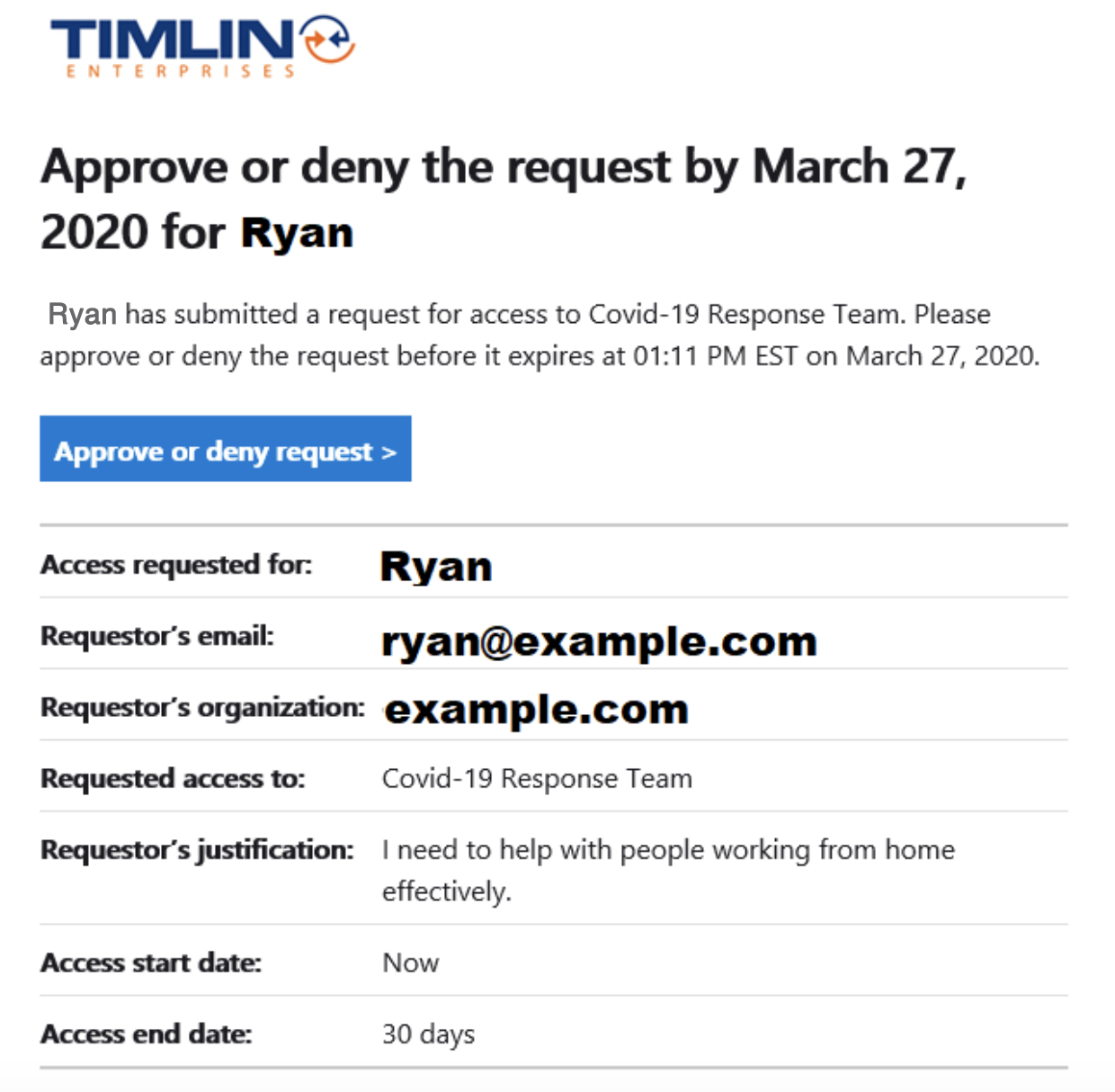
Pressing the Approve or deny request button takes you to an Approvals page where you can approve or deny and provide the required justification.
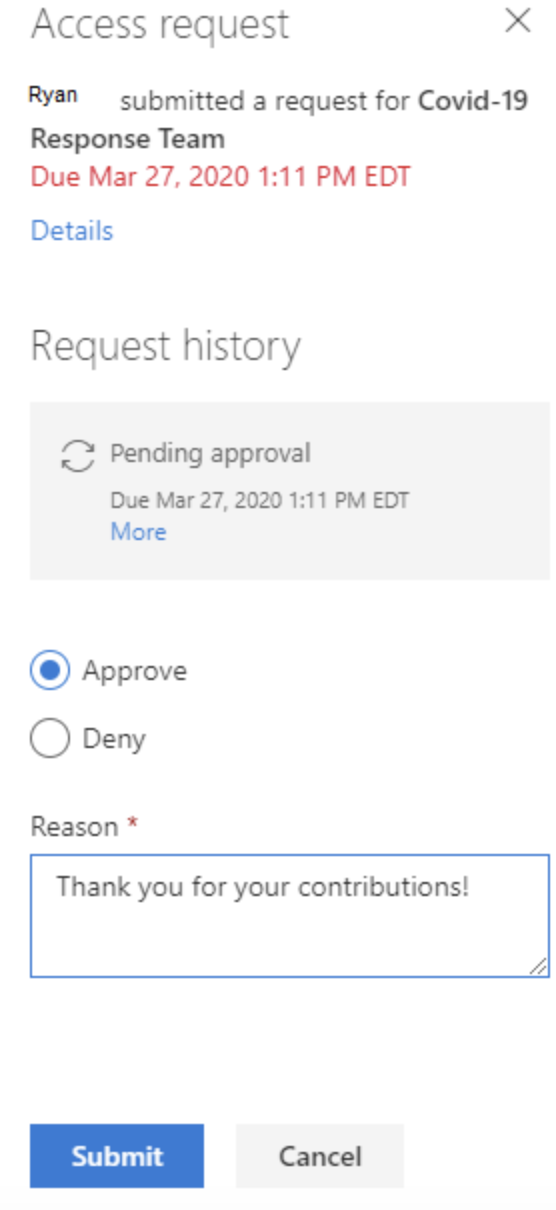
Now that the request has been approved, the user should have access to the Team as a Member. When the expiration date is reached in 30 days, that access will be revoked unless an extension is requested.
Summary
Entitlement Management using Access Packages is a great way to govern access to resources such as Teams, SharePoint sites, and Applications, especially when external users are involved or the context of the access is limited to a specific timeframe. Users can request access as needed, owners can be empowered to grant access on demand, and removal of access can be automated to prevent lingering exposure of company information.
Next up: Access Reviews
Configure periodic, guided reviews of access to resources with suggestions based on login activity and automated resolution based on dispositions.
